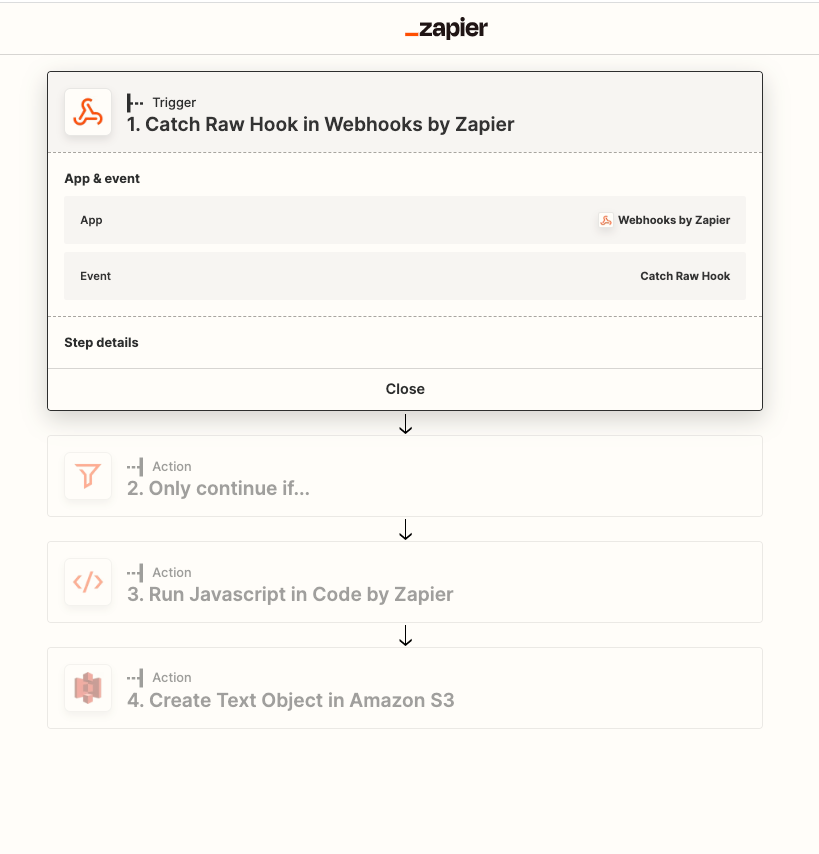
I am developing an app using the following flow:
- Catch Raw Hook (Zapier Provided URL).
- Parse data and compost a customized string.
- Send the data into S3 test object.
This is fronted by a serverless static S3 website form. All is well with the app except security team doesn’t agree that the Catch Raw Hook can be called from anywhere and anyone who has the url. (I agree too). They would like to see some kind of authentication on this #1 url. I took the time to research and came up with many discussions about these needs but doesn’t really give thorough instructions on how can be done.
These links includes:
All these links point to a “Possible with Zapier platform” But i guess i have couple of confusion with the platform…
first with the authentication. I can understand when you want to integrate a specific app to zapier, that app already have an authentication you piggy back off of that. But with my use case, I don’t have an app. Where is this authentication post pointing to in the authentication section? Do i need to create a diff custom api to front this authentication?
2nd, the zapier provided url is from the original zap describe in the flow. Do i lose this when I create a custom app with zapier platform? And on the trigger portion of the zapier platform, where do I point it to? Do i need to create a custom api to post this request to?
In my analysis, If i have to create a custom api for the platform to call to achieve the authentication and the action portion, then why do i need to use Zapier at all. My form can just call the custom api directly. It defeats the purpose.
Any advise, screenshots, direction on how to add authentication to catch raw webhook is appreciated.